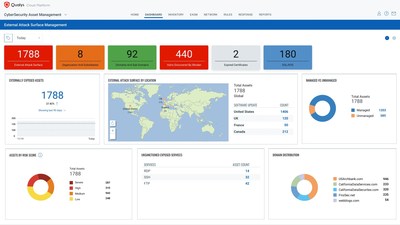
New capabilities in CyberSecurity Asset Management 2.0 enable security and IT teams to continuously discover unknown internet-facing assets and automatically assess their risk posture
Digital transformation, increased adoption of cloud and Internet of Things (IoT), a growing remote workforce, and a technology talent shortage have led to an exponential rise in organizations' attack surface. This expansion makes it harder for security teams to correlate externally visible and internally managed assets and govern compromises that occur because of undiscovered, unmanaged, or poorly managed IT assets. Organizations need a new approach to view vulnerable assets from the outside in and execute like an attacker to quickly identify areas of risk.
"Organizations must proactively manage their cyber defenses, which includes finding and addressing vulnerabilities to reduce cyber risk," said
"Qualys CyberSecurity Asset Management provides invaluable attack surface insights from an external attacker's point of view," said
Qualys CyberSecurity Asset Management 2.0 with EASM enables organizations to continuously monitor and reduce the entire enterprise attack surface including internal and internet-facing assets and discover previously unidentified exposures. It also helps synchronize with CMDBs, detect security gaps like unauthorized or end-of-support software, open ports, remotely exploitable vulnerabilities, digital certificate issues, unsanctioned apps and domains, and mitigate risk by taking appropriate actions.
Qualys CyberSecurity Asset Management with EASM allows Security and IT teams to:
Uncover Gaps Across the Entire Attack Surface - From a single cloud platform, the solution continuously discovers and accurately classifies internal and external internet-facing assets. It automatically finds your subsidiaries, performs horizontal and vertical domain and subdomain enumeration, correlates WHOIS and DNS records and attributes assets to your organization.
Get a Reliable, Accurate View Aligning Security and IT Ops - Augment uncertain, outdated data in your CMDB with CyberSecurity Asset Management. Teams can capture unmanaged assets and gain a single source of truth for internet-facing assets, along with location and context, through automatic synchronization with enterprise CMDBs and vulnerability management to streamline ongoing attack surface monitoring and response.
Rapidly Remediate Risk with Native VMDR 2.0 Integration - CyberSecurity Asset Management 2.0 and Qualys VMDR 2.0 improve the cybersecurity program posture with TruRisk scoring and automated and one-click orchestration of vulnerability and remediation workflows to convert internet-facing assets into fully managed and patched assets.
"Achieving full asset visibility remains one of cybersecurity's most elusive goals," said
Availability
Qualys CyberSecurity Asset Management 2.0 with EASM is currently in preview and available to existing customers. It will be generally available in mid-September. To request a free trial, visit qualys.com/csam-trial. Learn more by reading our blog, or attending our webinar on
Additional Resources
- Learn about CyberSecurity Asset Management 2.0
- Watch the video on CyberSecurity Asset Management 2.0 with EASM
- Read the CyberSecurity Asset Management product blog
- Details on the Qualys Cloud Platform
- Follow
Qualys on LinkedIn and Twitter
About
The Qualys Cloud Platform leverages a single agent to continuously deliver critical security intelligence while enabling enterprises to automate the full spectrum of vulnerability detection, compliance, and protection for IT systems, workloads and web applications across on premises, endpoints, servers, public and private clouds, containers, and mobile devices. Founded in 1999 as one of the first SaaS security companies,
Media Contact:
Jackie Dutton
Qualys
media@qualys.com
![]() View original content to download multimedia:https://www.prnewswire.com/news-releases/qualys-brings-external-attack-surface-management-easm-to-the-qualys-cloud-platform-301598646.html
View original content to download multimedia:https://www.prnewswire.com/news-releases/qualys-brings-external-attack-surface-management-easm-to-the-qualys-cloud-platform-301598646.html
SOURCE